A security vulnerability was discovered at GitHub back in 2012 that made it possible for an attacker to add new SSH keys to arbitrary GitHub user accounts. Although there was no known malicious activity using this exploit, they took the responsible step to email all their users that have SSH keys associated with their account to verify and approve them before they could be used to clone/pull/push repositories over SSH again.
Continue reading GitHub SSH Public Key Fingerprint CheckingCategory: Tips
Eclipse, EGit, github, jsch and AES-128 encrypted private keys
Here’s a tip if you are having trouble connecting to GitHub using Eclipse/Egit with a recently generated SSH key pair…
Continue reading Eclipse, EGit, github, jsch and AES-128 encrypted private keysJavascript Word Wrapping
I recently needed to do some manual word wrapping (and possibly hyphenation) of strings in JavaScript and found some interesting code projects:
- TypeSet – an implementation of the 1981 Knuth and Plass line breaking algorithm [PDF] using JavaScript and the HTML5 canvas element.
- “wordwrap” for JavaScript – A port of PHP’s wordwrap function.
- Hyphenator.js – client-side hyphenation of HTML-Documents
- Balance-text – A jQuery plugin for balancing wrapping text in a web page
Counting your top WordPress comment spam source IPs and URLs
I launched a new WordPress blog for a client a few months ago and have been watching as comment spammers find the site and do what they do best, leave spam. As the first few spam comments started coming in I would flag them then manually copy/paste the source IPs and URLs to the built-in WordPress “Comment Blacklist“.
Over time I obviously started seeing some duplicates and I noticed bursts of spam from certain IPs or linking to specific spam URLs. I was curious to see what these top IPs and URLs were, as they would seem the best candidates to include in the blacklist.
So, let’s dig around in the database a bit…
Continue reading Counting your top WordPress comment spam source IPs and URLsManually triggering Google Apps account transition
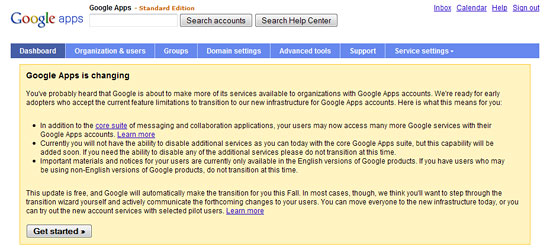
If you want to be an early adopter, and haven’t already automatically been given the option to transition your Google Apps account to the new infrastructure, here’s a handy tip to manually trigger the upgrade process.
Point your browser to the following URL, using your own Google Apps domain name, like so:
https://www.google.com/a/cpanel/[yourdomain.name]/GoogleAccountUpgrade

